The cyber threats that challenge global energy systems

Op-ed: Digitalization is hot. Really hot. The global analysis institute Gartner predicts that 2018 will become the year that digitalization moves down the hype cycle from the current "Peak of Inflated Expectations" to the unavoidable "Trough of Disillusionment."
In the energy sector, big data, advanced analytics and artificial intelligence offer hope of better utilization of already installed capacity, as systematic analysis of the huge amounts of data generated by power generators, transmission systems, and distribution networks can be used to increase efficiency and decrease costs.
Data is sent from the many sensors built into the sector's heavy machinery and wiring to its industrial control systems. The acquired knowledge is compared with historical data for the same or similar systems, and maintenance teams are sent to address identified issues. Everything is connected through the Internet of Things.
Increasing vulnerability to hackers
The possibilities are many, but the linking of hundreds or even thousands of instruments, all connected over the Internet, gives rise to whole new concerns: Global energy systems are increasingly threatened by hackers.
The threat from cyber attacks has risen dramatically over recent years, both in terms of number and extent. Robert Hannigan, who until recently was Director of the British Government Communications Headquarters, GCHQ, in charge of the British government's attempt to curb cyber crime, is not in doubt: Russian state-sponsored actors are seeking to destabilize western democracies through destructive attacks on critical national infrastructure, the North Korean dictatorship steals money, and Chinese groups steal strategic information about technologies and business models. All in cyberspace.
Denmark has the world's best energy system. The country recently received top marks in the World Energy Council's survey of national energy systems. A key reason for this top position for the energy system overall was the top position for energy security, where Denmark took the number one place. But this position cannot be taken for granted. The Danish Center for Cyber Security under the Defense Intelligence Service concluded, around the same time as the World Energy Council report was published in December 2017, that the biggest threat to the country's national security is cyber attacks.
In particular, attacks on critical national infrastructure, such as energy systems, are worrying. The stability of an energy system can quickly be challenged. There are three different "flanks" that should be kept under strict observation.
The first flank: the energy companies themselves
The first flank is the energy companies themselves. They may come under direct attack.
This happened in Ukraine the day before Christmas in 2015. Three distribution companies were hacked at the same time, and the hackers managed to turn off electrical power for a quarter of a million people for several hours. On the web, there are several video clips that show how the control systems in the companies' control rooms were "owned" by hackers. The cursor simply moved around the screen while the staff was watching helplessly.
The explanation that this is possible at all is to be found in recent years of rapid development within the technical components that constitute the power generation, transmission, and distribution network. Large parts of this network are controlled by so-called SCADA systems. SCADA (Supervisory Control And Data Acquisition) systems are used to control the energy network and retrieve data from this. The challenge with SCADA systems and other industrial control systems is that the machines they control are simply not designed with cyber security in mind.
For example, the security of a massive generator has so far been the difficulty in getting near its control systems. An attacker would have to crawl over the fence of a power plant, sneak unnoticed through the doors, and gain physical access to the room where the control system was located. It was virtually impossible, and the security of the system itself was therefore not perceived as important. This has changed over just a few years.
Today, almost all SCADA systems are connected to the Internet, so the security of the system itself has become extremely important. But the industry that produces these large machines and their associated SCADA systems has not developed security systems at the same rate as the machines have been connected to the Internet, so many systems with insufficient security are today installed in global energy systems.
The second flank: the suppliers
The second flank that should be kept under observation is the supply chain. It may also come under attack.
The German industrial giant Siemens, which supplies many of the machines used in the energy sector and many other sectors, announced in November 2017 that it had been compromised by Chinese hackers for several years. The company explicitly stated that its energy division was among the affected entities. The concern in the energy sector is, of course, that global energy systems have installed components in which Trojan horses or other malware lies dormant as ticking bombs.
Weaknesses in supply chain networks can also quickly become weaknesses in the energy system network itself. Many of the installed SCADA systems remain connected to the suppliers' networks, even after transferring ownership of the equipment to the energy companies. This allows vendors to retrieve data from the installed machines, which can contribute to a deeper understanding of the machines and improved designs, but it also creates a new opportunity for hackers: In addition to the energy companies' own networks, hackers can access machines through suppliers' networks. Multiple access points must be protected against attacks.
The third flank: indirect damage by attacks aimed at others
The third and last flank is difficult to manage. The energy system can become "collateral damage" in an attack on other sectors, i.e. it can suffer damage in connection with attacks that are not targeted at the energy sector itself.
This happened to the world's biggest carrier of seaborne freight, transporting about 15 percent of all global trade by containers, AP Moller-Maersk in June 2017. The company's business units in the logistics sector (Maersk Line, APM Terminals, and Damco) became "collateral damage" in a cyber attack in connection with the ongoing conflict between Russia and Ukraine. The computer virus "NotPetya" was spread to Maersk's network through a compromised update of the accounting software MeDoc, which the company used to pay taxes in Ukraine. This cost Maersk somewhere between USD 200 and 300 million, mainly due to lost revenues the following month, where IT systems were operating suboptimally or were completely down.
Maersk was not the actual target of the attack. The virus was, according to statements made by the UK and US governments last month, primarily targeted at Ukraine's financial, energy and government sectors as part of the Kremlin's ongoing effort to destabilize the country. But the malicious software did not discriminate: It destroyed everything on its way, including Maersk's IT systems. Such attacks are terribly hard to protect against.
The ability to recover systems
Precisely because it is so hard to prevent cyber attacks, several leading experts, including Robert Hannigan, advocate for increased focus on cyber resilience – that is, the ability to quickly and efficiently restore systems that have been hacked.
The argument is that larger companies simply can not expect that their hundreds or thousands of employees all – every single day – act flawlessly against the many cyber threats, why such companies should expect to be hacked from time to time. When prevention is very difficult, recovery management may be a better investment.
The ultimate code breaker technology
Increased digitalization of the energy sector is accompanied by increased cyber security challenges. Energy companies that seek to exploit new technologies to create new business opportunities, as described above, are at the same time making themselves more vulnerable to cyber attacks.
But what's worse: The attackers also make use of new technologies. It is already possible for criminals to find vulnerabilities in IT systems using robotic process automation. It is also already possible to attack these vulnerabilities systematically and vigorously using artificial intelligence.
However, cryptographic methods that can secure information when transmitted over the Internet do exist, so although difficult, it is not impossible to protect sensitive information. In the near future, we cannot even take this for granted. The ultimate code breaking technology is soon ready for commercial use: The quantum computer is in rapid development.
The quantum computer differs fundamentally from "classical" computers in the same way as quantum physics differs from classical physics. Classical computers store information in and execute algorithms on bits that can take the value one or zero. Quantum computers store information in and execute algorithms on qubits that can take the value one or zero as well as all so-called "coherent superpositions" of these. Oversimplifying, one could say that the classical bit can be either one or zero, while the quantum mechanical qubit can be both one and zero at the same time. This opens new opportunities for calculating in radically different ways.
Shors algorithm is perhaps the most well-known algorithm written with the quantum computer in mind. The algorithm is able to factorize large numbers in a highly efficient manner. Try multiplying 13 by 19. It is not difficult: The result is 247. Try then to find the two factors (integer numbers) that multiplied with each other gives the result 391. It is quite difficult; the answer is 17 multiplied by 23. This problem is solved by Shor's algorithm, not just for small three-digit numbers, as in the examples above, but for huge numbers greater than one billion billion billion.
This algorithm is extremely interesting for hackers, since most current cryptographic systems used for money transfers and other sensitive communications are based on the fact that it is difficult to factorize large numbers obtained through multiplication of major prime numbers. (Did you notice that the factors above were all prime numbers?) In other words, by using Shor's algorithm, the quantum computer can break most modern cryptographic systems.
The universal quantum computer that will make this technology widely available is expected to become commercially available within 10-15 years. IBM's research program in the field, called IBM Q, is among the world's leading and has a five-qubit quantum computer running in its lab. The ultimate code breaker technology is no longer science fiction. It is within reach. And it is a scary new weapon in the hands of the already well-equipped hackers.
The end of cyber security?
Is that the end of cyber security? Not necessarily.
A number of existing cryptography algorithms are believed to be secure against attacks from quantum computers, e.g. various symmetric cryptographic algorithms and cryptographic hash functions. Another quantum technology, which can guarantee 100 percent secure communications, is also far ahead in its development: Quantum key distribution systems are already commercially available.
The key message to companies and regulators involved with global energy systems is not to panic and overreact today, but rather to reflect about what will be required in the not-so-far future. When deciding to invest in new power capacity in 2018, which will likely be built in the early-2020s, transferred to operations in the mid-2020s, and operated until the mid-2050s, it would be wise to consider the impact of the quantum computer and take steps to protect core networks.
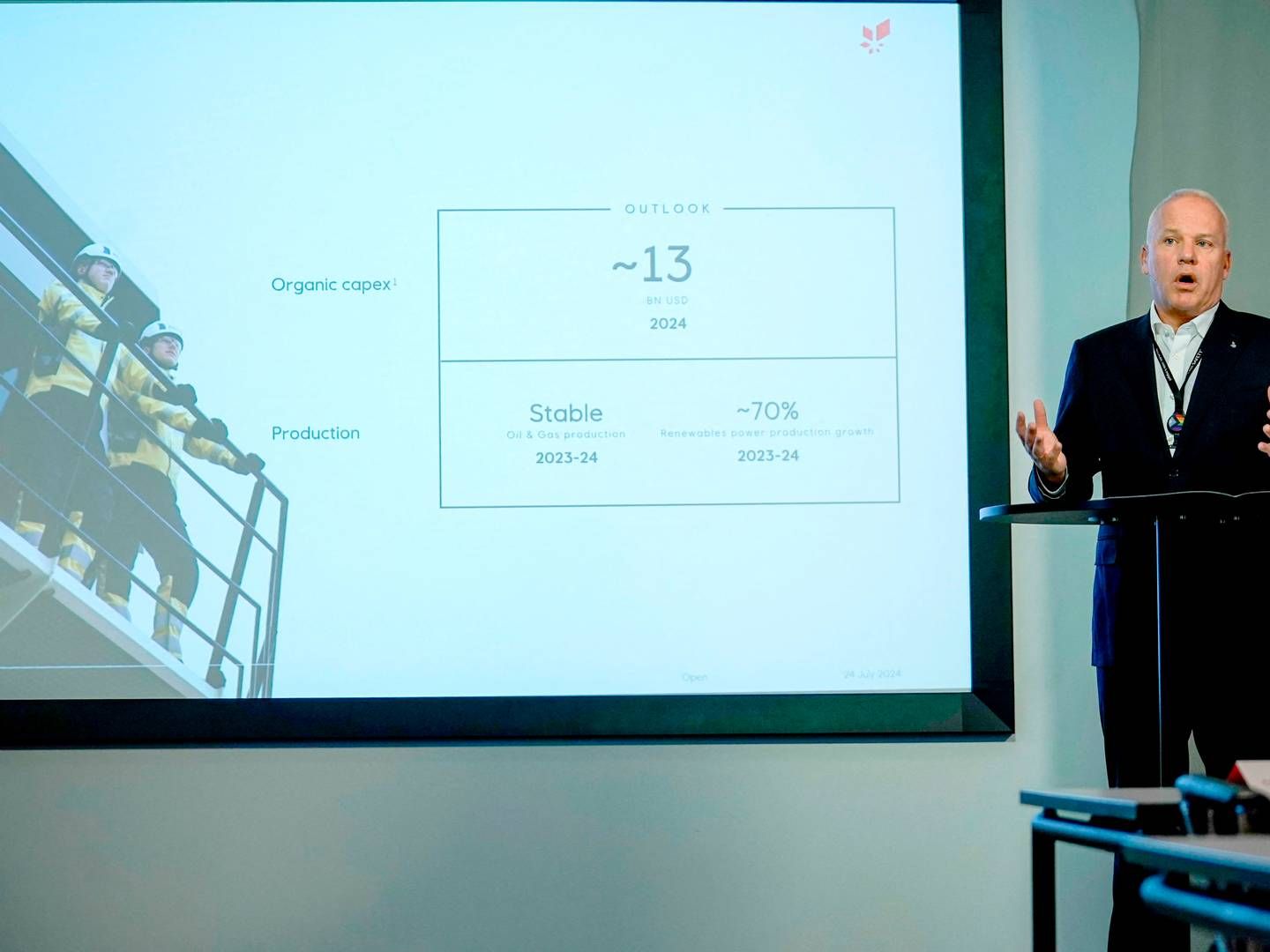
Morten Stilling is Chief Digitalization Officer at Ørsted, one of the leading companies in offshore wind energy globally. He leads Ørsted’s efforts to digitalize wind farm construction and operations. He also leads efforts to increase Ørsted’s ability to defend against cyber threats targeting wind farm control systems.
Stilling holds a Master’s Degree in engineering and a Ph.D. in computational quantum physics. Before joining Ørsted, he worked with strategy consulting firm McKinsey & Company and energy/shipping company Maersk.
Focus on cyber threat against energy in new Danish defense agreement
Related articles
Norwegian wind power set record despite average winds
For subscribers
Ørsted in "exclusive discussions" about a major sale
For subscribers